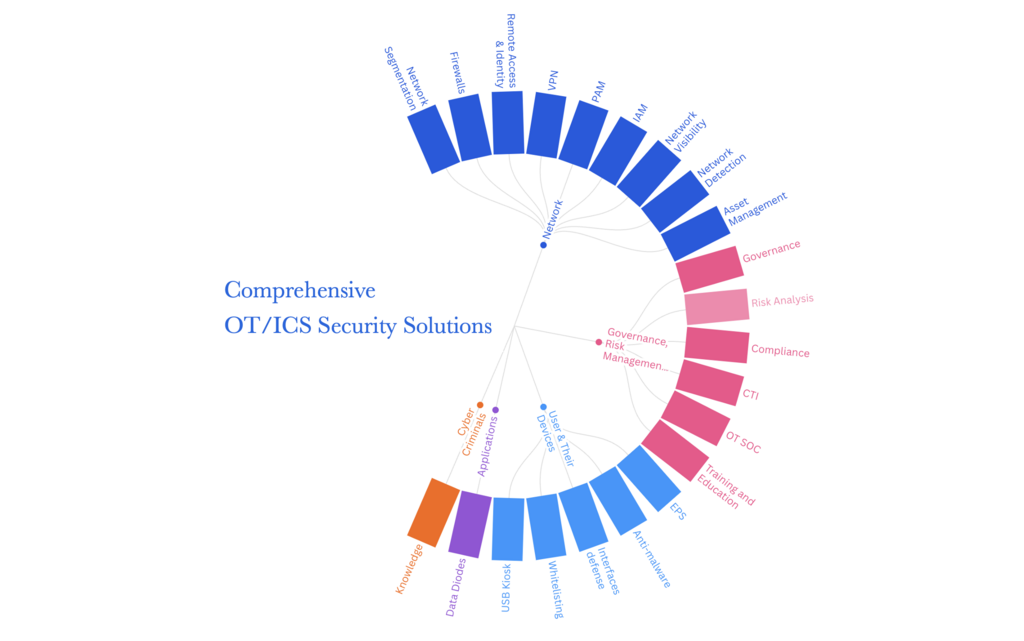
Comprehensive OT/ICS cybersecurity solutions designed to protect critical infrastructure from evolving threats while maintaining operational continuity.
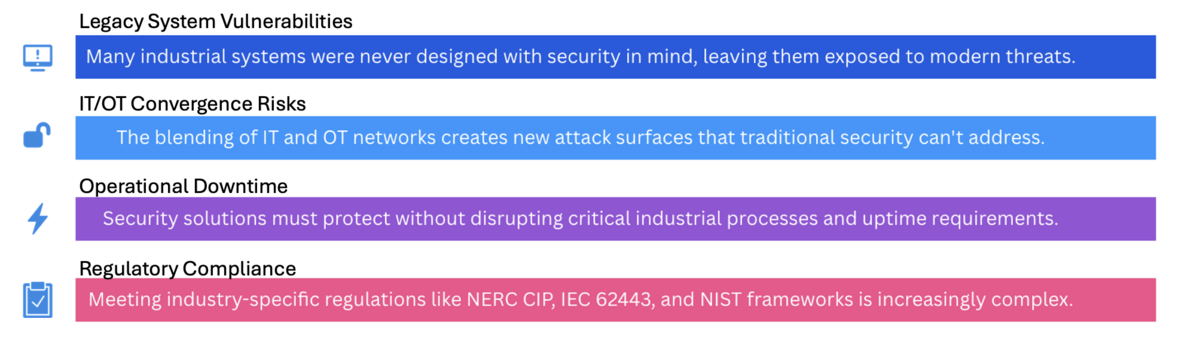
Industrial environments face unique cybersecurity challenges that require specialized solutions.
Our team of OT security experts is ready to help you assess risks and implement the right protection for your critical infrastructure.
With decades of experience securing critical infrastructure, we understand the unique requirements of industrial environments.
Our team includes former plant operators and control engineers who speak your language.
Deployed Secure Zone and Conduit Architecture, MITRE EMB3D-based OT threat detection, ICS/SCADA threat modelling and risk assessment, OT SOC design and upcoming MDR services.
Solutions designed to meet ISA/IEC 62443, NIST CSF, NERC CIP, and other industry standards.
Built to Defend Against the Real Adversaries
Nation-states. Ransomware gangs. Supply chain intrusions. We align your defenses to the tactics real attackers use—like logic injection (TO889), lateral movement (TO866), and remote access exploitation (TO859).
Learn more about protecting your industrial systems with our latest insights.

Microsoft has emphasized the need for securing internet-exposed operational technology (OT) devices following a spate of cyber attacks targeting such environments since late 2023.

Cybersecurity researchers have discovered what they say is the ninth Industrial Control Systems (ICS)-focused malware that has been used in a disruptive cyber attack targeting an energy company
Cybersecurity researchers have disclosed 46 new security flaws in products from three solar power system vendors, Sungrow, Growatt, and SMA, that could be exploited by a bad actor to seize control of devices or execute code remotely, posing severe risks to electrical grids.
We are a Singapore based OT/IACS cybersecurity solution provider with over a decade of cybersecurity experience securing critical infrastructure across diverse critical infrastructure sectors including energy, critical manufacturing, water treatment, transportation, building automation, and etc. Our team combines deep operational technology expertise with comprehensive information security knowledge to deliver holistic protection for the systems that power our modern world. Our OT/ICS cybersecurity offerings now reach clients across the Asia-Pacific regions.
Our mission is simple: protect the systems that run the world.
With extensive expertise in ISA/IEC 62443, NIST CSF, NIST SP800-82, CSA CCoP, ISO27001 ISMS, ISO/IEC 42001, MITRE ATT&CK for ICS, and MITRE EMB3D regulatory compliance, standards and frameworks, we design and implement adversary-informed, standards-aligned security programs specifically tailored for industrial environments. From sophisticated zone and conduit architecture design to advanced logic integrity monitoring, real-time threat detection, and comprehensive OT-SOC enablement—we deliver robust defense mechanisms that perform reliably under demanding real-world operational conditions. What sets us apart is execution. We've worked inside the plant, not just the boardroom. We understand the intricate balance required to protect production systems without disrupting critical operations. Our practitioners have hands-on experience with industrial control systems, understanding the unique challenges of securing environments where availability and safety are paramount.
We partner with operators of critical systems to solve the cybersecurity challenges that matter most—delivering solutions that are not only technically sound but also operationally viable. Our approach is always collaborative, working closely with plant operators, IT teams, and executive leadership to ensure security measures enhance rather than hinder operational efficiency.
Our comprehensive methodology encompasses risk assessment, security architecture design, implementation support, staff training, and ongoing monitoring. We deliver defense strategies that work safely, securely, and at scale, ensuring that critical infrastructure remains resilient against evolving cyber threats while maintaining operational excellence.

Copyright © 2025 Certisec Pte. Ltd.. All rights reserved.